
Unparalleled security
Redwall Mobile® uses unique patented techniques to protect against threats from within and without. While other vendors work on patches for malware like KingRoot or bugs like Stagefright, Redwall devices have been safe all along. No updates required, no emergency patching.
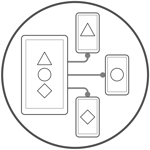
Multi-mission, multi-persona
Dual persona simply doesn't cut it anymore. Redwall Mobile with Secure Persona® allows for any number of distinct personas, each with its own securely isolated apps, data, settings, authentication requirements, and policy that defines which processes can access which system features, drivers, files, and networks.
Quick info
Looking for quick information on Redwall Technologies product? Below are some of the brief introductory materials to get you started:- Redwall Company Overview Brochure.pdf - A brief but complete introduction to Redwall Technologies and our flagship product, Redwall Mobile®
- Redwall Company Overview Presentation.pdf - A short slide deck on Redwall Mobile's core technology and the issues it addresses
Visit the downloads page for more detailed papers and slide decks, and please contact us at sales@redwall.us if we can answer any questions or to arrange a demonstration.
Multi-mode
Redwall Mobile is the only technology that can create multiple cryptographically and temporally isolated personas on a single device, and enforce both high-level and granular security policies outside of the operating system.

IoT / Vehicles
Redwall's patented IoT security technology is embedded into devices to prevent unauthorized access, block threats both from the network or other interfaces as well from within the device, and ensure device integrity and authenticity.

Mission-critical
Redwall's patented multi-layered approach has proven to be completely resistant to zero-day threats that have penetrated other mobile and embedded defenses with ease, making it suitable for your mission-critical devices.
Did you know...
- Redwall Mobile can perform attestation on a device, run device-level integrity checks, and take advantage of any trusted boot features.
- Redwall Mobile security policies are simple to create, and can be edited using the policy server or with any JSON editing tool.
- Redwall works with industry partners to offer a variety of 8(a) contract vehicles.
- Redwall Mobile can operate with or without a server (MDM) component, and is suitable for tactical, non-connected (disconnected) deployments.
- Interested in partnering? Redwall frequently partners with both defense primes and other small businesses.

